Note to the reader
First of all thank you for visiting the English version of the website edoardolimone.com. The site has over 470 articles that deal with cybersecurity, artificial intelligence, digitization. Translating all the material takes a lot of time and for this reason not all the content has been translated into other languages. It is a gradual process that aims to safeguard quality and costs. If an article of interest has not yet been translated, please be patient or, in the meantime, use one of the online translators.
Thank you for your patience and trust.
Edoardo Limone

Between data breaches and embarrassing communications
A few months after the entry into force of NIS 2, security shortcomings continue to be found in many commercial sectors that are impacted by the European Directive and beyond;

War and Peace: I.A. in warfare
The purpose of this article is to reflect on how artificial intelligence can be used in a war context and subsequently introduced into a civil operational environment.

Contracts and artificial intelligence
The purpose of this article is to suggest a simple and functional approach to cataloguing the risks arising from the implementation of artificial intelligence within organisations.

Risk Management and Artificial Intelligence
The purpose of this article is to show the evolution of ISO 27005, to present a compatible and alternative methodological paradigm for cyber risk management, and to observe some of

The Culture of Safety – Part 2
Italy is facing an increasing number of cyber threats both in quantity and complexity, yet there seems to be no equally effective evolution in terms of cybersecurity. Let us try
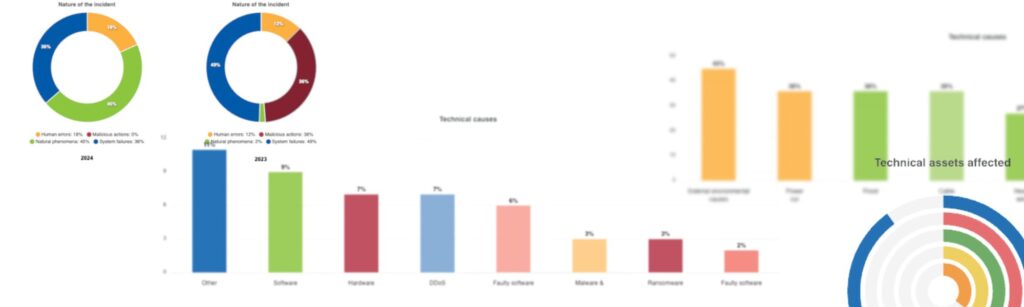
CIRAS: tracking cyber incidents in Europe
The European Union has an IT incident analysis tool called CIRAS. Let’s take a look at this not always well known tool.

The future of Europe and the world
In these hours stadium choruses are rising on social networks for and against the self-styled agreement with Elon Musk’s Space X company, wanted by Prime Minister Giorgia Meloni.

Cyber Anti-Sec 2024
Welcome to the ‘Cyber Anti-Sec’ security report covering the year 2024, in which the most relevant data, trends and data breaches will be analysed.

Data breach: AIAD
AIAD is the Federation, member of Confindustria, representing Italian Aerospace, Defence and Security Companies.

Data breach: INPS Servizi S.p.A.
The company INPS Servizi S.p.A. was the subject of a data breach by the LYNX collective, with data exfiltration and interruption of services. Let’s find out more.

NIS 2: General Considerations
NIS 2 is bringing a number of compliance activities by private companies and public administrations, sometimes not very consistent with the regulations. Let us try to make some reflections on

The culture of data management
The Equalize case is filling the front pages of the national press and is spreading like wildfire. On social media, it is being talked about in a very technical way,

Data breach Postel S.p.A.: the provision of the Garante
The newsletter of the Garante per la Protezione dei Dati Personali (Italian Data Protection Authority) publicises as news measure No. 572 of 4 July 2024 concerning the data breach suffered

NIS 2: a possible case of compulsive standardisation
On 17 October, Italy will transpose the NIS 2 Directive(CELEX EU 2022/2555), and the expectation surrounding this directive raises a doubt: will the directive have any real usefulness or have

The usefulness of technology
For a few months now, we have been beginning to read articles that seem to re-propose the importance of certain technologies that have been much talked about until now. Among

Cyber attacks in countries with low economic development
The idea that hackers only target the most industrially powerful countries is wrong; certainly the United States, China, Europe, are constantly at the centre of cyber attacks, but there are

The arrest of Pavel Durov
A lot of information is circulating these hours about the arrest of the founder of the messaging service Telegram: Pavel Durov. Not all this information is correct, let’s try to

Regulations and Managing a Data Breach
On 26 July 2024, the Agency for National Cybersecurity (ACN) published the ‘Guide to Reporting Incidents to CSIRT Italy’. It is a 56-page document that gathers some interesting information that

Data breach: Bucci-Olmi notary firm
The Everest Group hit a notary firm and this data breach is likely to have truly dramatic connotations considering the type of target and the amount of data exfiltrated. Let

The point on health data breaches
In Italy, there is a major problem in restoring health services following a computer incident, and it matters little whether the incident is caused by negligence or malicious intent. In

Technology and energy consumption
We are constantly talking about technologies such as blockchain and artificial intelligence, but we also have to assess the energy consumption and pollution related to their deployment. Let us try to get into the numbers with the aim of understanding the real importance of these technologies but also the heavy impact they have on the environment and available resources. We must use them wisely!
Artificial intelligence and online violence on animals and children
After the analysis carried out in 2021 and reported in the article‘Videos of animal violence are increasing on the net‘, it was decided to return to the subject a few

What is DWELL TIME in cybersecurity
It is a term little known to the uninitiated, but dwell time is perhaps one of the most important elements to know for those working in cybersecurity.

Data breach: Azienda Socio Sanitaria Territoriale Rhodense
Another data breach to the detriment of public health has hit the Lombardy region, this time it is the turn of ASST Rhodense, let’s try to understand what happened.
